Further Put up Contributors: Maxime Peim, Benoit Ganne
Cloud-VPN & IKEv2 endpoints exposition to DoS assaults
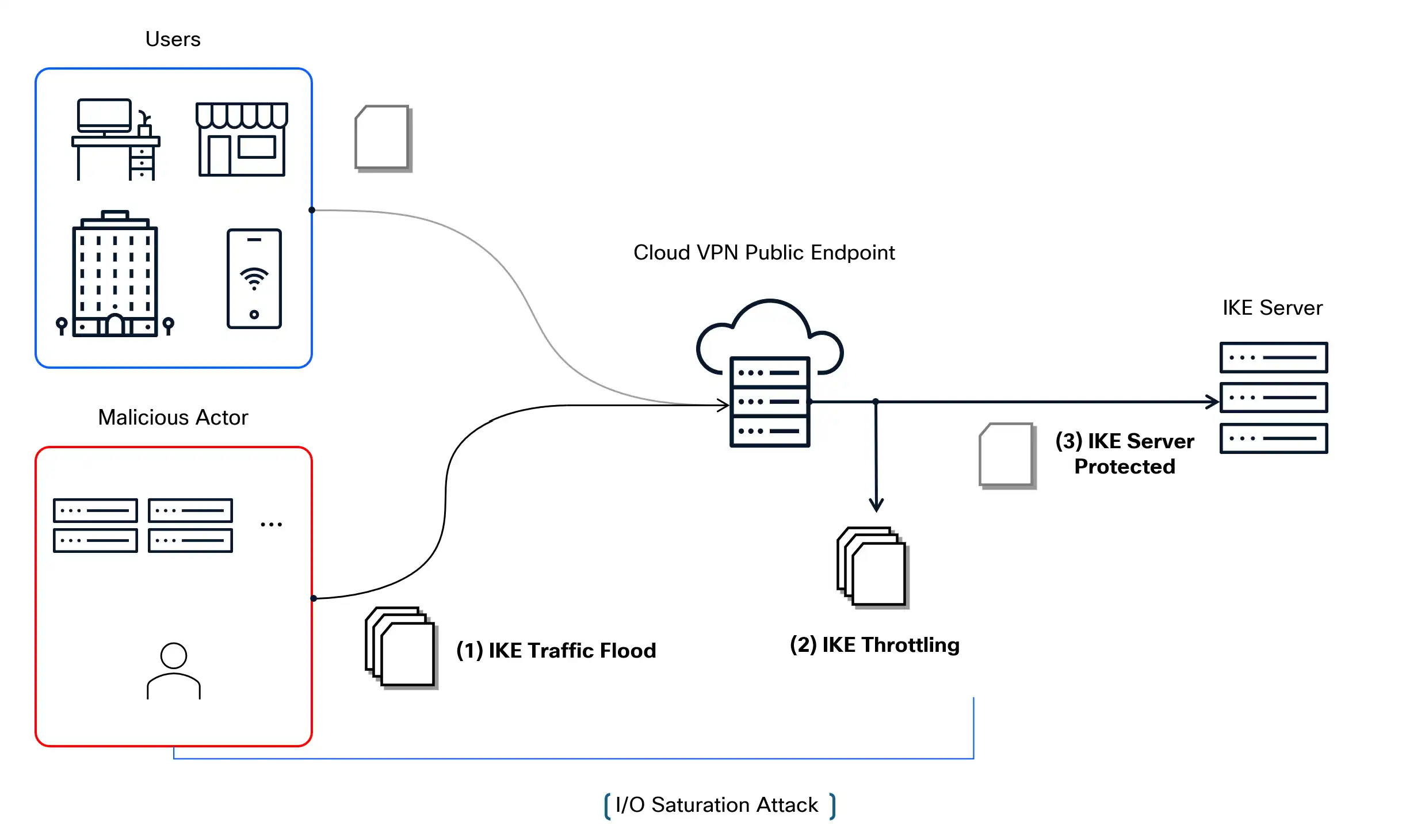
Cloud-based VPN options generally expose IKEv2 (Web Key Trade v2) endpoints to the general public Web to assist scalable, on-demand tunnel institution for patrons. Whereas this allows flexibility and broad accessibility, it additionally considerably will increase the assault floor. These publicly reachable endpoints grow to be engaging targets for Denial-of-Service (DoS) assaults, whereby adversaries can flood the important thing trade servers with a excessive quantity of IKE site visitors.
Past the computational and reminiscence overhead concerned in dealing with giant numbers of session initiations, such assaults can impose extreme stress on the underlying system by excessive packet I/O charges, even earlier than reaching the applying layer. The mixed impact of I/O saturation and protocol-level processing can result in useful resource exhaustion, thereby stopping professional customers from establishing new tunnels or sustaining current ones — in the end undermining the supply and reliability of the VPN service.
Implementing a network-layer throttling mechanism
To reinforce the resilience of our infrastructure towards IKE-targeted DoS assaults, we carried out a generalized throttling mechanism on the community layer to restrict the speed of IKE session initiations per supply IP, with out impacting IKE site visitors related to established tunnels. This strategy reduces the processing burden on IKE servers by proactively filtering extreme site visitors earlier than it reaches the IKE server. In parallel, we deployed a monitoring system to establish supply IPs exhibiting patterns in keeping with IKE flooding conduct, enabling fast response to rising threats. This network-level mitigation is designed to function in tandem with complementary safety on the utility layer, offering a layered protection technique towards each volumetric and protocol-specific assault vectors.
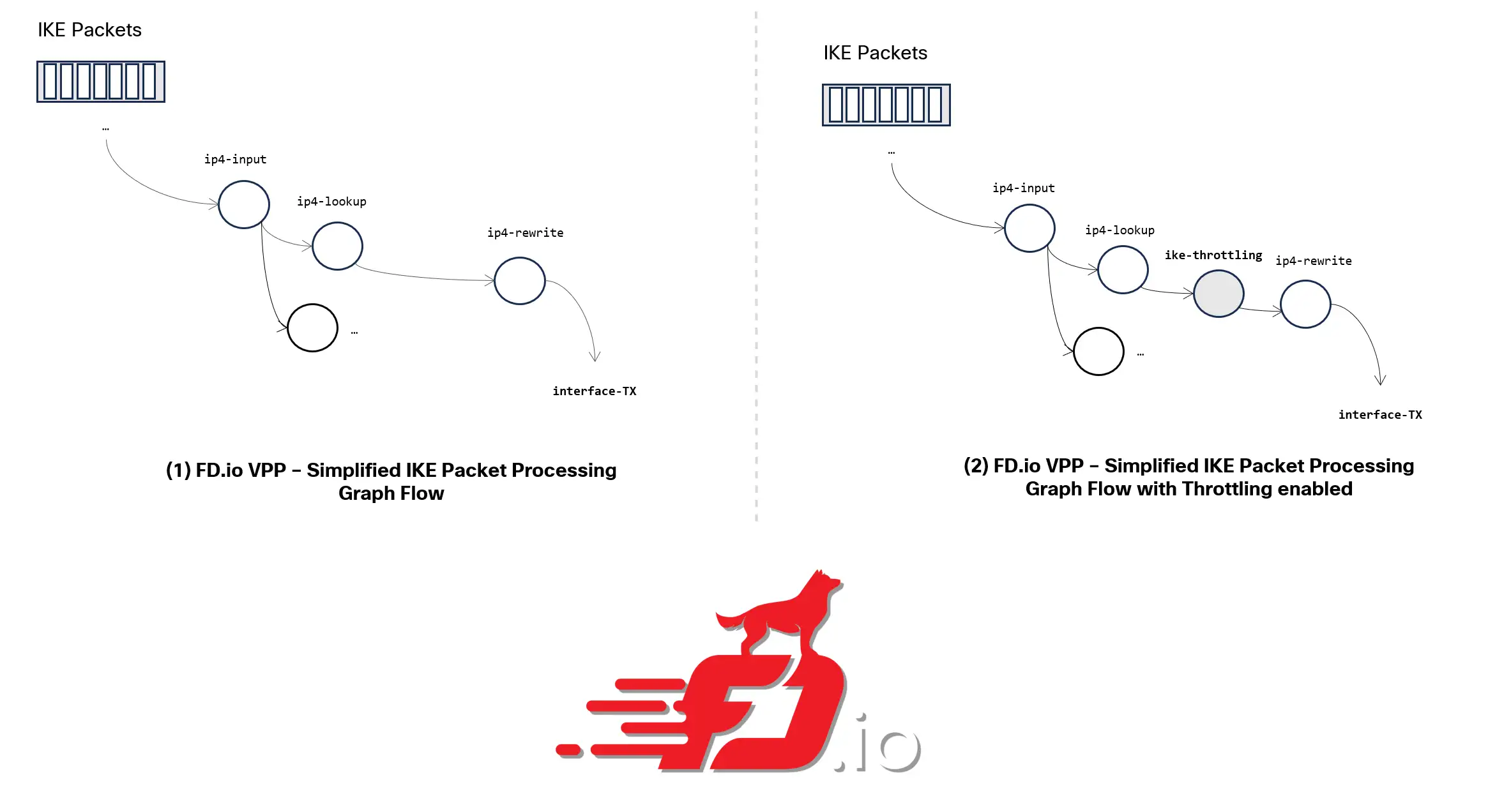
The implementation was carried out in our data-plane framework (primarily based on FD.io/VPP – Vector Packet processor) by introducing a brand new node within the packet-processing path for IKE packets.
This practice node leverages the generic throttling mechanism out there in VPP, with a balanced strategy between memory-efficiency and accuracy: Throttling choices are taken by inspecting the supply IP addresses of incoming IKEv2 packets, processing them right into a fixed-size hash desk, and verifying if a collision has occurred with previously-seen IPs over the present throttling time interval.

Minimizing the affect on professional customers
Occasional false positives or unintended over-throttling could happen when distinct supply IP addresses collide throughout the identical hash bucket throughout a given throttling interval. This case can come up attributable to hash collisions within the throttling information construction used for price limiting. Nonetheless, the sensible affect is minimal within the context of IKEv2, because the protocol is inherently resilient to transient failures by its built-in retransmission mechanisms. Moreover, the throttling logic incorporates periodic re-randomization of the hash desk seed on the finish of every interval. This seed regeneration ensures that the likelihood of repeated collisions between the identical set of supply IPs throughout consecutive intervals stays statistically low, additional decreasing the probability of systematic throttling anomalies.

Offering observability on high-rate initiators with a probabilistic strategy
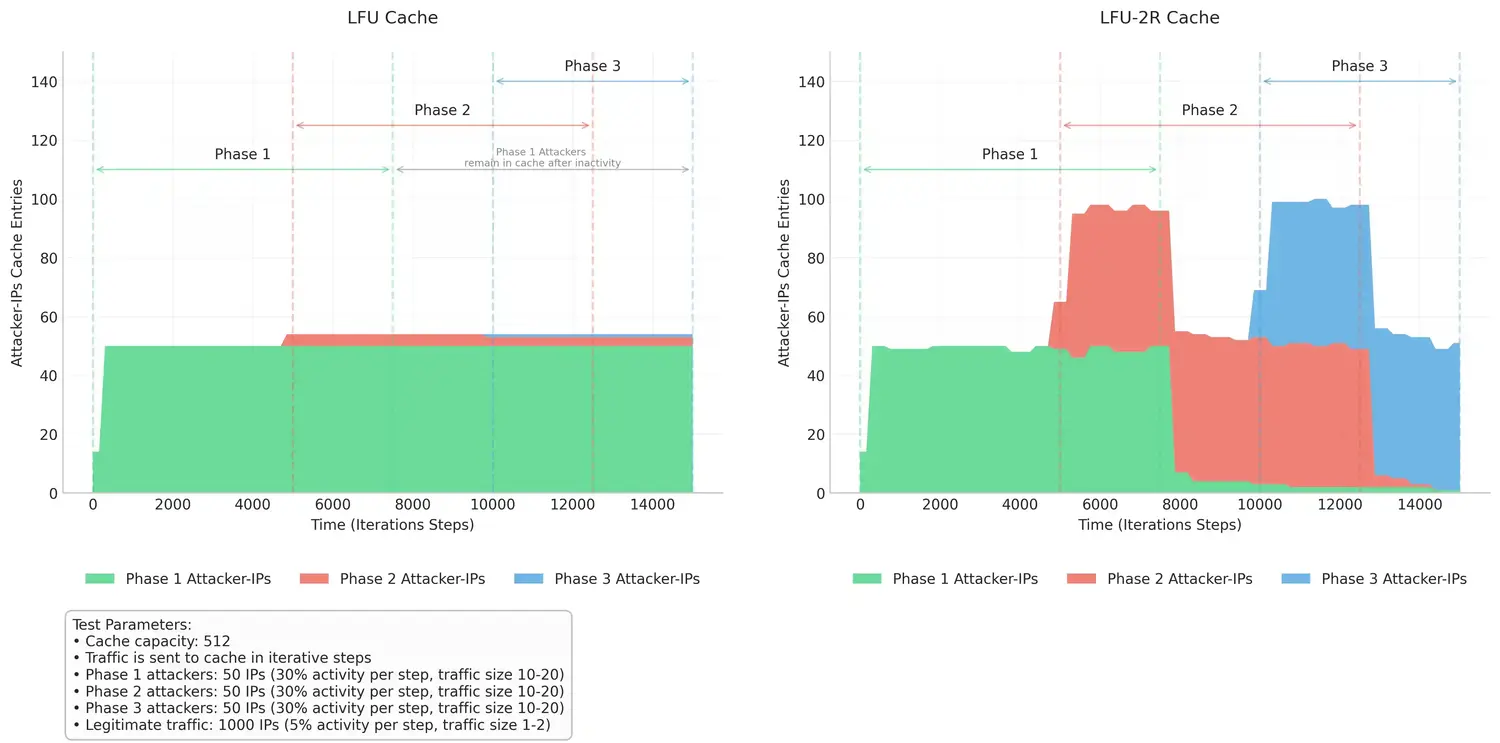
To enhance the IKE throttling mechanism, we carried out an observability mechanism that retains metadata on throttled supply IPs. This gives essential visibility into high-rate initiators and helps downstream mitigation of workflows. It employs a Least Steadily Used (LFU) 2-Random eviction coverage, particularly chosen for its steadiness between accuracy and computational effectivity beneath high-load or adversarial situations akin to DoS assaults.
Reasonably than sustaining a totally ordered frequency record, which might be pricey in a high-throughput information aircraft, LFU 2-Random approximates LFU conduct by randomly sampling two entries from the cache upon eviction and eradicating the one with the decrease entry frequency. This probabilistic strategy ensures minimal reminiscence and processing overhead, in addition to quicker adaptation to shifts in DoS site visitors patterns, making certain that attackers with traditionally high-frequency don’t stay within the cache after being inactive for a sure time frame, which might affect observability on more moderen energetic attackers (see Determine-6). The info collected is subsequently leveraged to set off extra responses throughout IKE flooding eventualities, akin to dynamically blacklisting malicious IPs and figuring out professional customers with potential misconfigurations that generate extreme IKE site visitors.
Closing Notes
We encourage comparable Cloud-based VPN companies and/or companies exposing internet-facing IKEv2 server endpoints to proactively examine comparable mitigation mechanisms which might match their structure. This might enhance techniques resiliency to IKE flood assaults at a low computational price, in addition to gives essential visibility into energetic high-rate initiators to take additional actions.
We’d love to listen to what you suppose! Ask a query and keep linked with Cisco Safety on social media.
Cisco Safety Social Media
Share:

